Get a fast solution to remove D0glun Ransomware and get technical assistance with decryption of .@D0glun@[original_extension] files. Download an effective removal tool and perform a full scan of your PC.
What is D0glun Ransomware
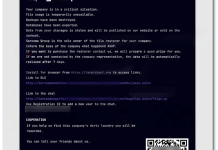
D0glun Ransomware is a particularly menacing type of malware classified as ransomware, designed to encrypt the victim’s files and hold them hostage in exchange for a ransom. This malicious software targets a wide spectrum of file types, including documents, images, and videos, disrupting personal and business operations. Upon infection, the ransomware appends a specific and distinct extension to the affected files following the pattern .@D0glun@[original_extension], visibly altering the filenames and rendering the files inaccessible. Its encryption algorithm is highly advanced, often utilizing a combination of symmetric and asymmetric cryptography, making decryption without the attacker’s involvement nearly impossible. Following the encryption process, victims are left with a pop-up window or altered desktop wallpaper displaying a ransom note, written in gibberish if the Chinese alphabet is not installed, informing them of the situation and directing them to pay a ransom in Bitcoin. This ransom note is strategically placed to ensure it is prominently seen, adding pressure to the victim’s decision-making process.
你的文件已被加密
我的電腦出了什么向題? 您的電腦部分文件被我加密保存了 文件炎型有zip|rar|png|jpg|txt|mp4|等等各種常見文桂文件
在未解密前,請勿嘗試任何系毒軟件,否則我元法保証你的文件安全
我垓如何恢夏我的重要文件?
請下載To r瀏覽器,在你的右逍 然后訪向以下地址
hxxp://33333333h45xwqlf3s3eu4bkd6y6bjswva75ys7j6satex5ctf4pyfad.onion
尋求幫助 這是我的BTC收款地址
1M7JVws3HccTGd14CV3qX21G7gzcJj77UHAttempting to find a solution for decryption brings unfortunate news: currently, no free decryption tools are available for D0glun Ransomware. This means the encrypted files, denoted by the .@D0glun@[original_extension] suffix, remain inaccessible without the decryption key held by the attackers. It is critical, however, to resist the temptation to pay the ransom, as doing so does not guarantee file recovery and merely funds further ransomware development. To protect against such dire circumstances, the best practice is to maintain regular backups stored securely in multiple locations. For those already affected, manual decryption attempts through third-party tools might be futile and could potentially cause further data corruption. Instead, focus should be placed on removing the ransomware from the system to prevent additional encryptions and consulting online communities or forums for any new breakthroughs in decryption methodologies. As of now, utilizing robust cybersecurity strategies is essential to safeguard against this and similar ransomware threats.

How D0glun Ransomware infects computers
D0glun Ransomware infiltrates computers primarily through deceptive tactics that exploit user behavior and system vulnerabilities. This malware often arrives via phishing emails, which trick users into downloading malicious attachments or clicking on harmful links. These emails are cleverly disguised to appear as legitimate communications from trusted sources, increasing the likelihood of user interaction. Once the malicious file is executed, the ransomware is installed on the system, often without the user’s knowledge. Additionally, D0glun may leverage compromised websites or drive-by downloads, where simply visiting an infected site can trigger the download of the ransomware. The malware can also spread through unsafe download channels, such as peer-to-peer networks and unofficial software distribution sites, where users might inadvertently download bundled malicious software.
- Download D0glun Ransomware Removal Tool
- Get decryption tool for .@D0glun@[original_extension] files
- Recover encrypted files with Stellar Data Recovery Professional
- Restore encrypted files with Windows Previous Versions
- Restore files with Shadow Explorer
- How to protect from threats like D0glun Ransomware
Download Removal Tool
To remove D0glun Ransomware completely, we recommend you to use SpyHunter 5. It detects and removes all files, folders, and registry keys of D0glun Ransomware. The trial version of SpyHunter 5 offers virus scan and 1-time removal for FREE.
Alternative Removal Tool
To remove D0glun Ransomware completely, we recommend you to use Norton Antivirus from Symantec. It detects and removes all files, folders, and registry keys of D0glun Ransomware and prevents future infections by similar viruses.
D0glun Ransomware files:
pop-up window
{randomname}.exe
D0glun Ransomware registry keys:
no information
How to decrypt and restore .@D0glun@[original_extension] files
Use automated decryptors
Download Kaspersky RakhniDecryptor

Use the following tool from Kaspersky called Rakhni Decryptor, that can decrypt .@D0glun@[original_extension] files. Download it here:
There is no purpose to pay the ransom because there is no guarantee you will receive the key, but you will put your bank credentials at risk.
Dr.Web Rescue Pack
Famous antivirus vendor Dr. Web provides free decryption service for the owners of its products: Dr.Web Security Space or Dr.Web Enterprise Security Suite. Other users can ask for help in the decryption of .@D0glun@[original_extension] files by uploading samples to Dr. Web Ransomware Decryption Service. Analyzing files will be performed free of charge and if files are decryptable, all you need to do is purchase a 2-year license of Dr.Web Security Space worth $120 or less. Otherwise, you don’t have to pay.
If you are infected with D0glun Ransomware and removed from your computer, you can try to decrypt your files. Antivirus vendors and individuals create free decryptors for some crypto-lockers. To attempt to decrypt them manually, you can do the following:
Use Stellar Data Recovery Professional to restore .@D0glun@[original_extension] files

- Download Stellar Data Recovery Professional.
- Click Recover Data button.
- Select the type of files you want to restore and click Next button.
- Choose the location where you would like to restore files from and click Scan button.
- Preview found files, choose ones you will restore and click Recover.
Using Windows Previous Versions option:
- Right-click on infected file and choose Properties.
- Select Previous Versions tab.
- Choose a particular version of the file and click Copy.
- To restore the selected file and replace the existing one, click on the Restore button.
- In case there are no items in the list, choose an alternative method.
Using Shadow Explorer:
- Download Shadow Explorer program.
- Run it, and you will see a screen listing of all the drives and the dates that shadow copy was created.
- Select the drive and date that you want to restore from.
- Right-click on a folder name and select Export.
- In case there are no other dates in the list, choose an alternative method.
If you are using Dropbox:
- Login to the Dropbox website and go to the folder that contains encrypted files.
- Right-click on the encrypted file and select Previous Versions.
- Select the version of the file you wish to restore and click on the Restore button.
How to protect computer from viruses, like D0glun Ransomware, in future
1. Get special anti-ransomware software
Use ZoneAlarm Anti-Ransomware
Famous antivirus brand ZoneAlarm by Check Point released a comprehensive tool, that will help you with active anti-ransomware protection, as an additional shield to your current protection. The tool provides Zero-Day protection against ransomware and allows you to recover files. ZoneAlarm Anti-Ransomware is compatible with all other antiviruses, firewalls, and security software except ZoneAlarm Extreme (already shipped with ZoneAlarm Anti-Ransomware) or Check Point Endpoint products. The killer features of this application are: automatic file recovery, overwrite protection that instantly and automatically recovers any encrypted files, file protection that detects and blocks even unknown encryptors.
2. Back up your files

As an additional way to save your files, we recommend online backup. Local storage, such as hard drives, SSDs, flash drives, or remote network storage can be instantly infected by the virus once plugged in or connected to. D0glun Ransomware uses some techniques to exploit this. One of the best services and programs for easy automatic online backup is iDrive. It has the most profitable terms and a simple interface. You can read more about iDrive cloud backup and storage here.
3. Do not open spam e-mails and protect your mailbox

Malicious attachments to spam or phishing e-mails are the most popular method of ransomware distribution. Using spam filters and creating anti-spam rules is good practice. One of the world leaders in anti-spam protection is MailWasher Pro. It works with various desktop applications and provides a very high level of anti-spam protection.