What is LokerAdmin Ransomware
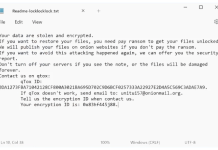
If you no longer can access your data then this may be because of file-encryption virus that could suddenly penetrate your system. Being categorized as ransomware, LokerAdmin encrypts user’s data by using AES algorithms and consequently demands a ransom in BTC to retrieve the locked files. LokerAdmin covers a range of data such as MS Office, PDFs, text files, images, music, videos, and archives which appear to be the most valuable for regular users. The encryption of files will visually result in icon and extension changes, internal changes are much more dramatic. First versions of the malware used .$$$ and .texyz suffixes. The latest variations switched to random 5-6 character alphanumerical sequences, like .8NWm8Y. For example, 1.mp4 will loose its original icon and migrate to 1.mp4.$$$ or 1.mp4.texyz file extensions. After successful encryption, the virus is hardwired for creating a note containing the ransom information (readme.txt).
To restore files write to the mail: lokeradmin@cock.li
If we dont respond within 24 hours - write to the mail: adminsysloker@airmail.cc
In subject: f12338491f
If you dont write immediately - the price will be higher.
To restore files write to the mail: UneGarc0n1@cock.li
If we dont respond within 24 hours - write to the mail: LeJetepreY0@cock.li
In subject: 80722510f2
If you dont write immediately - the price will be higher.
Unlike other ransomware, you will not see the information about the payment. Instead, they force you into writing to the attached e-mail to get further instructions on how to restore your data. Obviously, after sending a message, they will bill a certain amount of BTC that has to be paid within 24 hours, otherwise, they will raise the price. As you understand, it is risky to contact extortionists and pay the ransom. Of course, they are 100% able to give your files back, but it is not guaranteed that they will keep their promises. Instead, a better option would be uninstalling LokerAdmin from your device and restoring the ciphered data from an external backup.

How LokerAdmin Ransomware infected your computer
Ransomware-type infection can be spread via abusing vulnerable RDP configurations, fake e-mail campaigns with malicious attachments, trojans, botnets, keyloggers, exploits, web-injectors, and other dubious channels. Nonetheless, the most popular that wins amongst others is e-mail spam. Frauds send a multitude of scripted messages that contain ostensibly legitimate information and attached files as well. Such files can range multiple formats, but they are all for the same purpose – infiltrate the system of careless users’. Never open suspicious documents or links that you are not familiar with. Otherwise, you will experience an immediate malware infection like ransomware that will endanger your privacy. Other abovementioned channels can also soar up the risk of getting infected by ransomware. Luckily, we are here to help you uninstall the LokerAdmin Ransomware from your computer with the full guideline presented below.
- Download LokerAdmin Ransomware Removal Tool
- Get decryption tool for .$$$ or .texyz files
- Recover encrypted files with Stellar Data Recovery Professional
- Restore encrypted files with Windows Previous Versions
- Restore files with Shadow Explorer
- How to protect from threats like LokerAdmin Ransomware
Download Removal Tool
To remove LokerAdmin Ransomware completely, we recommend you to use Norton Antivirus from Symantec. It detects and removes all files, folders and registry keys of LokerAdmin Ransomware and prevents future infections by similar viruses.
Alternative Removal Tool
To remove LokerAdmin Ransomware completely, we recommend you to use SpyHunter 5. It detects and removes all files, folders and registry keys of LokerAdmin Ransomware. The trial version of Spyhunter 5 offers virus scan and 1-time removal for FREE.
LokerAdmin Ransomware files:
32_NOTRASH.EXE
readme.txt
z.bat
{randomfilename}.exe
LokerAdmin Ransomware registry keys:
no information
How to decrypt and restore .$$$ or .texyz files
Use automated decryptors
Download Kaspersky RakhniDecryptor

Use following tool from Kaspersky called Rakhni Decryptor, that can decrypt .$$$ or .texyz files. Download it here:
There is no purpose to pay the ransom because there is no guarantee you will receive the key, but you will put your bank credentials at risk.
Dr.Web Rescue Pack
Famous antivirus vendor Dr. Web provides free decryption service for the owners of its products: Dr.Web Security Space or Dr.Web Enterprise Security Suite. Other users can ask for help in the decryption of .$$$ or .texyz files by uploading samples to Dr. Web Ransomware Decryption Service. Analyzing of files will be performed free of charge and if files are decryptable, all you need to do is purchase a 2-year license of Dr.Web Security Space worth $120 or less. Otherwise, you don’t have to pay.
If you are infected with LokerAdmin Ransomware and removed it from your computer you can try to decrypt your files. Antivirus vendors and individuals create free decryptors for some crypto-lockers. To attempt to decrypt them manually you can do the following:
Use Stellar Data Recovery Professional to restore .$$$ or .texyz files

- Download Stellar Data Recovery Professional.
- Click Recover Data button.
- Select type of files you want to restore and click Next button.
- Choose location where you would like to restore files from and click Scan button.
- Preview found files, choose ones you will restore and click Recover.
Using Windows Previous Versions option:
- Right-click on infected file and choose Properties.
- Select Previous Versions tab.
- Choose particular version of the file and click Copy.
- To restore the selected file and replace the existing one, click on the Restore button.
- In case there is no items in the list choose alternative method.
Using Shadow Explorer:
- Download Shadow Explorer program.
- Run it and you will see screen listing of all the drives and the dates that shadow copy was created.
- Select the drive and date that you want to restore from.
- Right-click on a folder name and select Export.
- In case there are no other dates in the list, choose alternative method.
If you are using Dropbox:
- Login to the DropBox website and go to the folder that contains encrypted files.
- Right-click on the encrypted file and select Previous Versions.
- Select the version of the file you wish to restore and click on the Restore button.
How to protect computer from viruses, like LokerAdmin Ransomware, in future
1. Get special anti-ransomware software
Use ZoneAlarm Anti-Ransomware
Famous antivirus brand ZoneAlarm by Check Point released a comprehensive tool, that will help you with active anti-ransomware protection, as an additional shield to your current protection. The tool provides Zero-Day protection against ransomware and allows you to recover files. ZoneAlarm Anti-Ransomware is compatible with all other antiviruses, firewalls, and security software except ZoneAlarm Extreme (already shipped with ZoneAlarm Anti-Ransomware) or Check Point Endpoint products. The killer features of this application are: automatic file recovery, overwrite protection that instantly and automatically recovers any encrypted files, file protection that detects and blocks even unknown encryptors.
2. Back up your files

As an additional way to save your files, we recommend online backup. Local storages, such as hard drives, SSDs, flash drives or remote network storages can be instantly infected by the virus once plugged in or connected to. LokerAdmin Ransomware uses some techniques to exploit this. One of the best services and programs for easy automatic online backup is iDrive. It has the most profitable terms and simple interface. You can read more about iDrive cloud backup and storage here.
3. Do not open spam e-mails and protect your mailbox

Malicious attachments to spam or phishing e-mails is most popular method of ransomware distribution. Using spam filters and creating anti-spam rules is good practice. One of the world leaders in anti-spam protection is MailWasher Pro. It works with various desktop applications, and provides very high level of anti-spam protection.