What is Mac Cryptominer
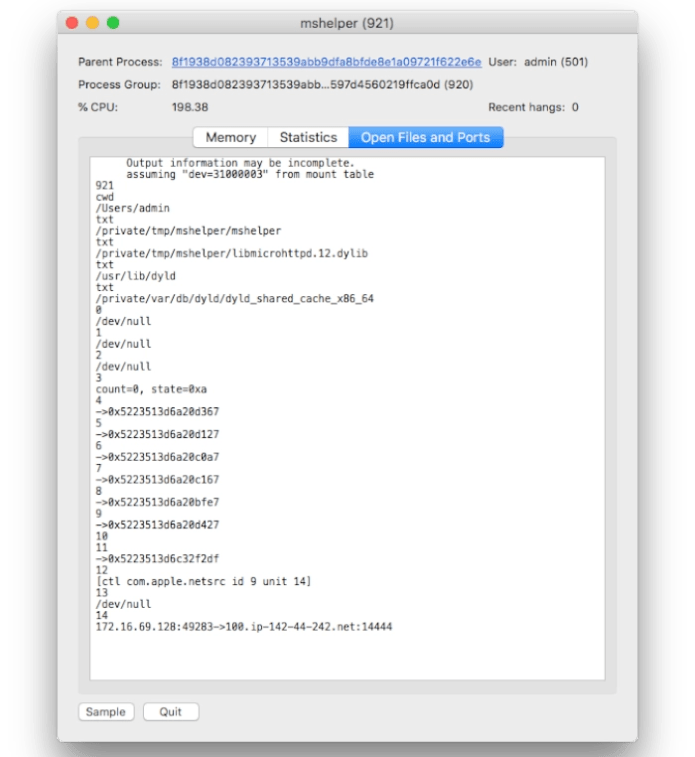
Mac Cryptominer is a type of malware that infiltrates Mac systems to hijack computing resources for cryptocurrency mining without the user’s consent. This malicious software typically deploys stealthy tactics to run in the background, unnoticed, increasing the CPU workload significantly. As it utilizes a substantial portion of the system’s processing power, users may experience a noticeable slowdown in performance, frequent system crashes, and unexpected shutdowns due to overheating. This excessive resource consumption not only degrades the overall functionality of the device but also leads to increased electricity bills. Over time, the constant strain on hardware components can cause irreversible damage, necessitating costly repairs or replacements. The cryptominer typically infiltrates systems through bundled software downloads, fake update alerts, or malicious email attachments. To protect against such threats, users should exercise caution during software installations, avoid dubious download sources, and employ robust antivirus solutions to detect and eliminate potential infections.
How Mac Cryptominer infected your system
Mac Cryptominer viruses typically infiltrate computers through deceptive methods like bundled software installations, where malicious programs are hidden within legitimate applications. Users often unintentionally install these cryptominers when downloading free software from unofficial sources, as they tend to skip through installation steps without scrutinizing what is being added. Additionally, cybercriminals exploit phishing emails, which contain malicious attachments or links that execute scripts to download and install the malware. Fake software updates, especially for widely-used programs like Adobe Flash Player, are also a common vector; users are tricked into believing their software is outdated and unknowingly install the cryptominer. Social engineering tactics, such as alarming pop-ups or misleading advertisements, further facilitate the spread of these viruses by manipulating users into downloading harmful software. To avoid infection, it is crucial to download software only from official sites, be cautious of email attachments from unknown senders, and utilize reputable antivirus tools.
Download Removal Tool for Mac
To remove Mac Cryptominer completely, we recommend you to use SpyHunter for Mac. It can help you remove files, folders, malicious profiles from Mac and uninstall add-ons from the Safari browser. The trial version of SpyHunter for Mac offers virus scan and 1-time removal for FREE.
Alternative Removal Tool
To remove Mac Cryptominer completely, we recommend you to use CleanMyMac. It can help you remove files, folders, malicious profiles of Mac Cryptominer, and get rid of unwanted add-ons from the Safari browser.
Remove Mac Cryptominer from macOS manually
Removing Mac Cryptominer from macOS requires a systematic approach that involves a combination of built-in tools, safe computing practices, and sometimes third-party software. Here’s a comprehensive guide to identifying and removing viruses from your Mac, ensuring your system’s integrity and security.
Step 1: Disconnect from the Internet
- Disconnect your Mac from the Internet. This prevents the virus from sending data to its creator or downloading more malicious software. Turn off Wi-Fi and unplug any Ethernet cables.
Step 2: Enter Safe Mode
- Restart your Mac in Safe Mode. Safe Mode performs a check of your startup disk and restricts certain software from automatically loading or opening.
- For Intel-based Macs: Restart your Mac and immediately press and hold the Shift key until you see the login window.
- For Apple Silicon Macs: Turn off your Mac, press and hold the power button until you see the startup options window, select your startup disk, press and hold the Shift key, then click Continue in Safe Mode.
Step 3: Use Built-in Tools for Malware Removal
- Use Finder to identify and remove suspicious applications.
- Open Finder, go to the Applications folder, and look for any applications you don’t recognize or didn’t intentionally download.
- Right-click the suspicious application and select Move to Trash, then empty the Trash.
- Use macOS built-in malware removal tool (MRT). macOS automatically runs MRT in the background, but you can manually run a malware scan by updating your software.
- Go to System Preferences > Software Update.
- Install any available updates, as these often include the latest security improvements and malware definitions.
Step 4: Check and remove Mac Cryptominer from Login Items
Note: Mac Cryptominer may set up to start on macOS startup. Therefore, before starting the removal, perform these steps:
- Open System Preferences, choose Users & Groups.
- Choose your account (set up as Current User).
- Click Login Items tab.
- Find suspicious entries. Select it, and click the “-“ (minus) button to remove them.
Step 5: Check and remove Mac Cryptominer Malicious Device Profile
Important update: Mac Cryptominer can install malicious Device Profile called AdminPrefs or similarly on MacOS, that won’t allow users to make changes to browser search engine and homepage settings. Follow instructions below to remove this profile.
Remove Mac Cryptominer profile
- Go to System Preferences and click on Profiles.
- In the list of profiles on the left side, choose AdminPrefs or other profile and click on “-” button to remove it.
- In your case it can be named differently, in this case remove all visible profiles. Check the picture below to see how it looks like.

Step 6: Reset Your Web Browsers
Reset Safari:
- Start Safari on your Mac, click Safari to open drop-down menu and choose Preferences
- Go to the Privacy section of Safari’s preferences.
- Click Remove All Website Data button.
- In the opened window, click Remove Now button to remove data stored by websites in Safari.
- Go to the Advanced section of Safari’s preferences.
- Click the Show Develop menu in menu bar option.
- In the menu, click Develop and select Empty Caches from this menu.
- Again, go to Safari menu and choose Clear History….
- Choose to clear all history and click Clear History button.
Reset Google Chrome:
- Start Google Chrome browser
- In address box type (or copy-paste)
chrome://settings. - Scroll down and find Show advanced settings link.
- Click on it and scroll down to the bottom again.
- Click Reset settings button and click Reset to confirm.
Reset Mozilla Firefox:
- Start Mozilla Firefox browser.
- In address box type (or copy-paste)
about:support. - Click Refresh Firefox… button.
- Click Refresh Firefox to confirm.
Step 7: Restore from a Backup
- If the issue persists, consider restoring your Mac from a backup.
- Use Time Machine or another backup system to restore your Mac to a state before it was infected.
- Ensure the backup you choose predates the malware infection.
Prevention Tips
- Keep your macOS updated. Regularly check for and install macOS updates to ensure you have the latest security patches.
- Be cautious with downloads and attachments. Only download software from trusted sources like the Mac App Store or official websites.
- Use strong passwords and enable two-factor authentication (2FA) where possible.
- Consider enabling the macOS firewall in System Preferences > Security & Privacy.
- Regularly back up your Mac using Time Machine or another backup solution to ensure you can recover your system if needed.
Following these steps should help you remove most viruses from your Mac. If you continue to experience issues, consider seeking help from Apple Support or a professional cybersecurity service.














