What is Redeemer Ransomware
Before getting to the removal, it is worth knowing what Redeemer Ransomware actually is. It is classified as a file-encrypting virus that blocks access to data stored on a compromised system. In order to show whether it is encrypted or not, Redeemer developers append the .redeem extension to each of the files. For instance, a file like 1.pdf will change its look to 1.pdf.redeem and reset its original icon. The system will no longer be able to open the files whilst they are encrypted. To return control over your data, it is necessary to buy special decryption software along with a unique key. More detailed information on that can be located inside of the Read Me.TXT note, which is created after encryption is over:
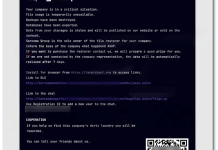
-- Redeemer -
All your files have been encrypted using an advanced encryption algorithm. They cannot be decrypted without a decryption tool and a key.
In order to decrypt your files you will need to pay 20 XMR (Monero). After paying you will get a tool and a key to decrypt your files.
You can find more information about Monero on getmonero.org and you can buy it from localmonero.co or any other website or use any cryptocurrency exchange that has Monero listed.
WARNING: Do not modify the files, don't change their names and locations, otherwise they won't be able to be decrypted.
AFTER you obtain the required amount of XMR, contact equilibriumfinancialsupremecy@gmail.com and send the following key:
-
Just below the Redeemer logo drawn from numbers, cybercriminals ask users to pay 20 XMR (Monero) cryptocurrency, which is about 4000$ for the decryption of data. Once you will be ready to do so, the next step is to contact extortionists attaching your personal ID key via their e-mail address (test@test.test). This is necessary to obtain the payment address for committing a transfer. As soon as they receive your decryption ransom, you should be given the promised tools to recover your data. Unfortunately, those who decide to pay the required amount may end up scammed in the end. This is the nature of most cybercriminals who spit on their promises no matter what. Unfortunately, despite it is indeed recommended against dealing with cybercriminals, they are the only hope to recover all of your data. This is because they are the figures who possess a private key for raising the cipher applied to each file. Unless you have backup copies of blocked data that were created and stored prior to the encryption, we cannot guarantee you will recover your data. Redeemer Ransomware wipes out shadow copies and other backups stored on your system, which makes the recovery process eventually useless. Despite this being bad news, you have to delete Redeemer Ransomware as soon as possible to prevent further encryption or even attacks on other devices. Follow our guide below to get rid of this virus completely.

How Redeemer Ransomware infected your computer
Virus attacks similar to Redeemer Ransowmare are usually implemented using malicious spam letters, unprotected RDP configuration, trojans, backdoors, keyloggers, fake software cracking tools, unreliable torrent downloads, and other suspicious content that can be downloaded from the web. As statistics show, the mostly-abused method has been e-mail spam with malicious attachments. This is a well-spread technique used by cybercriminals to cover wide numbers of victims. Specifically to make them open malicious files attached to ostensibly legitimate letters. Most extortionists disguise their messages as something legitimate to elevate the trust of victims. Whatever the message content is, there are often MS Office documents, PDFs, executables, or JavaScript files included right there. It is quite hard to say whether they are malicious by judging solely on their appearance. However, in case such files are forcefully asked to be open by senders, more likely they are containing malware. Better not risk and do not open such files for curiosity reasons. Simply delete the received message if you are unsure whether it is totally safe. Make sure to follow our guide below as there are many tips to secure yourself against such threats in the future.
- Download Redeemer Ransomware Removal Tool
- Get decryption tool for .redeem files
- Recover encrypted files with Stellar Data Recovery Professional
- Restore encrypted files with Windows Previous Versions
- Restore files with Shadow Explorer
- How to protect from threats like Redeemer Ransomware
Download Removal Tool
To remove Redeemer Ransomware completely, we recommend you to use SpyHunter 5. It detects and removes all files, folders, and registry keys of Redeemer Ransomware. The trial version of Spyhunter 5 offers virus scan and 1-time removal for FREE.
Alternative Removal Tool
To remove Redeemer Ransomware completely, we recommend you to use Norton Antivirus from Symantec. It detects and removes all files, folders, and registry keys of Redeemer Ransomware and prevents future infections by similar viruses.
Redeemer Ransomware files:
Read Me.TXT
{randomname}.exe
Redeemer Ransomware registry keys:
no information
How to decrypt and restore .redeem files
Use automated decryptors
Download Kaspersky RakhniDecryptor

Use following tool from Kaspersky called Rakhni Decryptor, that can decrypt .redeem files. Download it here:
There is no purpose to pay the ransom because there is no guarantee you will receive the key, but you will put your bank credentials at risk.
Dr.Web Rescue Pack
Famous antivirus vendor Dr. Web provides free decryption service for the owners of its products: Dr.Web Security Space or Dr.Web Enterprise Security Suite. Other users can ask for help in the decryption of .redeem files by uploading samples to Dr. Web Ransomware Decryption Service. Analyzing of files will be performed free of charge and if files are decryptable, all you need to do is purchase a 2-year license of Dr.Web Security Space worth $120 or less. Otherwise, you don’t have to pay.
If you are infected with Redeemer Ransomware and removed it from your computer you can try to decrypt your files. Antivirus vendors and individuals create free decryptors for some crypto-lockers. To attempt to decrypt them manually you can do the following:
Use Stellar Data Recovery Professional to restore .redeem files

- Download Stellar Data Recovery Professional.
- Click Recover Data button.
- Select type of files you want to restore and click Next button.
- Choose location where you would like to restore files from and click Scan button.
- Preview found files, choose ones you will restore and click Recover.
Using Windows Previous Versions option:
- Right-click on infected file and choose Properties.
- Select Previous Versions tab.
- Choose particular version of the file and click Copy.
- To restore the selected file and replace the existing one, click on the Restore button.
- In case there is no items in the list choose alternative method.
Using Shadow Explorer:
- Download Shadow Explorer program.
- Run it and you will see screen listing of all the drives and the dates that shadow copy was created.
- Select the drive and date that you want to restore from.
- Right-click on a folder name and select Export.
- In case there are no other dates in the list, choose alternative method.
If you are using Dropbox:
- Login to the DropBox website and go to the folder that contains encrypted files.
- Right-click on the encrypted file and select Previous Versions.
- Select the version of the file you wish to restore and click on the Restore button.
How to protect computer from viruses, like Redeemer Ransomware, in future
1. Get special anti-ransomware software
Use ZoneAlarm Anti-Ransomware
Famous antivirus brand ZoneAlarm by Check Point released a comprehensive tool, that will help you with active anti-ransomware protection, as an additional shield to your current protection. The tool provides Zero-Day protection against ransomware and allows you to recover files. ZoneAlarm Anti-Ransomware is compatible with all other antiviruses, firewalls, and security software except ZoneAlarm Extreme (already shipped with ZoneAlarm Anti-Ransomware) or Check Point Endpoint products. The killer features of this application are: automatic file recovery, overwrite protection that instantly and automatically recovers any encrypted files, file protection that detects and blocks even unknown encryptors.
2. Back up your files

As an additional way to save your files, we recommend online backup. Local storages, such as hard drives, SSDs, flash drives, or remote network storages can be instantly infected by the virus once plugged in or connected to. Redeemer Ransomware uses some techniques to exploit this. One of the best services and programs for easy automatic online backup is iDrive. It has the most profitable terms and a simple interface. You can read more about iDrive cloud backup and storage here.
3. Do not open spam e-mails and protect your mailbox

Malicious attachments to spam or phishing e-mails are the most popular method of ransomware distribution. Using spam filters and creating anti-spam rules is good practice. One of the world leaders in anti-spam protection is MailWasher Pro. It works with various desktop applications and provides a very high level of anti-spam protection.