How to stop “PayPal – You Added A New Address” e-mail spam
PayPal - You Added A New Address email spam is a deceptive phishing campaign designed to trick recipients into believing that a new address has been added to their PayPal account. These emails often create a sense of urgency, prompting users to take immediate action, such as calling a fake support number, which can lead to serious security breaches. Spam campaigns like this typically infect computers by enticing users to click on malicious links or download infected attachments, which can carry malware or trojans. Once opened, these malicious files can compromise the user's system, allowing cybercriminals to access sensitive information, steal personal data, or even take control of the device remotely. Additionally, some emails may appear to originate from legitimate sources by spoofing email addresses or using legitimate-looking graphics, which makes them harder to identify as fraudulent. Cybercriminals often leverage social engineering tactics to manipulate emotions and trick users into making poor security decisions. To combat such threats, it’s crucial for users to remain vigilant and skeptical of unsolicited emails, especially those requesting personal or financial information. Regularly updating antivirus software and avoiding interactions with suspicious emails can significantly reduce the risk of infection from these spam campaigns.
How to stop “Login From A New Device” e-mail spam
Login From A New Device email spam is a deceptive phishing attempt designed to trick recipients into providing their login credentials by falsely claiming that their account has been accessed from an unrecognized device. These emails often create a sense of urgency, prompting users to click on a provided link to secure their accounts, which leads them to a fraudulent website that mimics legitimate login pages. Once users enter their credentials, the information is captured by cybercriminals, who can then exploit stolen accounts for various malicious purposes, including identity theft and unauthorized financial transactions. Spam campaigns infect computers primarily through malicious links or attachments embedded in these deceptive emails. When users click on such links, they may be redirected to sites that automatically download malware onto their devices or request them to download infected files disguised as legitimate documents. Additionally, some malicious emails contain attachments that, when opened, execute harmful scripts or programs that compromise the user's system. Vigilance and a cautious approach towards unknown emails can significantly reduce the risk of falling victim to these scams and prevent potential infections.
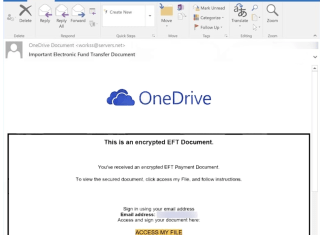
How to stop “OneDrive – Encrypted EFT Document” e-mail spam
OneDrive - Encrypted EFT Document email spam is a phishing scam that pretends to deliver an important electronic fund transfer document to recipients, enticing them to click on a link that leads to a fake OneDrive sign-in page. This deceptive tactic aims to steal personal information by prompting users to enter their email credentials, which are then captured by cybercriminals for malicious purposes. Spam campaigns like this often spread through indiscriminate email blasts, targeting numerous individuals without specific targeting. Once a user clicks on the link or opens an attachment within such spam, their computer can become infected with malware designed to extract sensitive data or perform unauthorized actions. Cybercriminals may use various tactics, including misleading subject lines and urgent messages, to increase the likelihood of engagement from unwary recipients. Additionally, these campaigns can leverage malicious attachments, which, when opened, can install malware on the user's system, further compromising their security. Protecting against such threats requires vigilance and the use of reputable security software to detect and eliminate potential infections before they can cause significant harm.
How to stop “Time Is Slipping Away From Your Grasp” e-mail spam
Time Is Slipping Away From Your Grasp email spam represents a type of sextortion scam where the sender falsely claims to possess compromising material obtained through malware supposedly planted on the recipient's device. This deceptive message aims to instill fear, suggesting that the sender has recorded private activities and demands payment in cryptocurrency to prevent the alleged exposure of this fabricated evidence. Spam campaigns like this typically infect computers by employing various tactics, such as enticing recipients to click on malicious links or download infected attachments. When users interact with these harmful elements, they may inadvertently download malware that can steal sensitive information, compromise online accounts, or even allow remote access to their devices. Scammers often utilize social engineering techniques, creating a sense of urgency or fear to manipulate victims into complying with their demands. Ignoring or engaging with such emails can lead to significant risks, making it essential for users to remain vigilant and cautious when dealing with unsolicited communications. Ultimately, protecting oneself from these threats involves employing reliable security software, practicing safe browsing habits, and being skeptical of unexpected emails.
How to stop “Loan Investment Opportunities For Your Business” e-mail spam
Loan Investment Opportunities For Your Business email spam is a deceptive solicitation that targets individuals by offering fraudulent investment opportunities, often claiming to help grow their businesses financially. These emails typically come from cybercriminals who use social engineering tactics to lure unsuspecting recipients into sharing sensitive personal information or making upfront payments disguised as fees. Spam campaigns can infect computers in various ways, with one common method involving malicious attachments or links embedded within these deceptive emails. When recipients click on these links or open infected attachments, they may inadvertently download malware that can compromise their systems. Additionally, some spam emails redirect users to compromised websites that automatically download malicious software to their devices. Cybercriminals exploit the urgency and allure of seemingly legitimate offers to increase the chances of successful infections. Consequently, recognizing and avoiding such scams is crucial for maintaining cybersecurity and protecting personal information.
How to stop “You’re Added To A New Group” e-mail spam
You're Added To A New Group email spam is a deceptive phishing campaign that falsely informs recipients they have been added to a workgroup, often luring them into clicking a malicious link that leads to a counterfeit login page. This type of scam aims to harvest victims' email account credentials and can result in significant privacy breaches, financial losses, and identity theft. Cybercriminals typically distribute these emails through mass campaigns, targeting thousands of users simultaneously with messages designed to invoke urgency or curiosity. Once a user interacts with the email—either by clicking links or downloading attachments—malware can be installed on their device, either directly or through the redirection to a compromised website. Malicious attachments may carry various forms of malware, including trojans that steal sensitive information, while some links may lead to sites where users unknowingly provide personal data. Even merely opening a spam email can compromise security, especially if it contains embedded links or files that exploit vulnerabilities in the user's software. Thus, it is crucial for individuals to exercise caution and utilize reliable antivirus protection to safeguard their systems against such threats.
How to stop “Quote That Meets Our Requirements” e-mail spam
Quote That Meets Our Requirements email spam is a deceptive phishing campaign designed to trick recipients into providing sensitive information by posing as a legitimate request for a quote. The email typically instructs users to click on a link to view requirements hosted on a fake file transfer site that mimics legitimate services like WeTransfer. Once users enter their login credentials on this fraudulent site, their information is captured by cybercriminals, leading to potential identity theft or unauthorized access to accounts. Spam campaigns often infect computers by distributing malicious files as attachments or through links that lead to harmful downloads. These emails can be crafted to appear genuine, utilizing logos and urgent language to create a sense of legitimacy, which increases the chances of users falling victim to the scam. Opening infected attachments or clicking on compromised links can initiate malware downloads, allowing attackers to steal sensitive data or gain control over the victim’s system. Regularly updating antivirus software and exercising caution when interacting with unsolicited emails are crucial steps in preventing such infections.
How to stop “Payment For Goods And Services” e-mail spam
Payment For Goods And Services email spam represents a deceptive phishing tactic where recipients receive messages claiming that a large payment for goods and services has been successfully processed. These emails typically include an attachment, often labeled something like "Payment Advice-stn_0027-1.pdf", which prompts users to open it for further details. This can lead to a phishing website that mimics legitimate services, capturing sensitive login credentials when users attempt to access their accounts. Spam campaigns infect computers primarily through malicious attachments or links embedded in the emails. When users open these attachments or click on the links, they may inadvertently download malware, such as trojans or ransomware, which exploit vulnerabilities in their systems. Cybercriminals often employ social engineering tactics to make these emails appear credible, increasing the likelihood that unsuspecting users will take the bait. Consequently, opening an infected attachment or clicking a harmful link can lead to severe privacy breaches, identity theft, and financial losses. Maintaining vigilance and employing robust security measures is essential to combat these pervasive threats effectively.